We are releasing OpenEverest 1.12 today. This is an expedited release focused on security.
The priority is patching CVE-2025-14847, also known as "MongoBleed." This is a critical vulnerability affecting MongoDB workloads running on Kubernetes.
If you run OpenEverest in production, we recommend upgrading to version 1.12 immediately to pull in the patched database images.
The Vulnerability: MongoBleed (CVE-2025-14847)
Disclosed by Wiz Research, CVE-2025-14847 is a high-severity, unauthenticated information leak in MongoDB Server.
The issue lies in the zlib network message decompression logic, which processes data before authentication.
- The Mechanism: An attacker sends a malformed compressed packet that tricks the server into mishandling the message length.
- The Leak: The server returns uninitialized heap memory to the client.
- The Risk: This memory can expose sensitive data, including authentication credentials or customer PII, without requiring a login.
Exploits for this vulnerability have been observed in the wild. You can read the full technical analysis here.
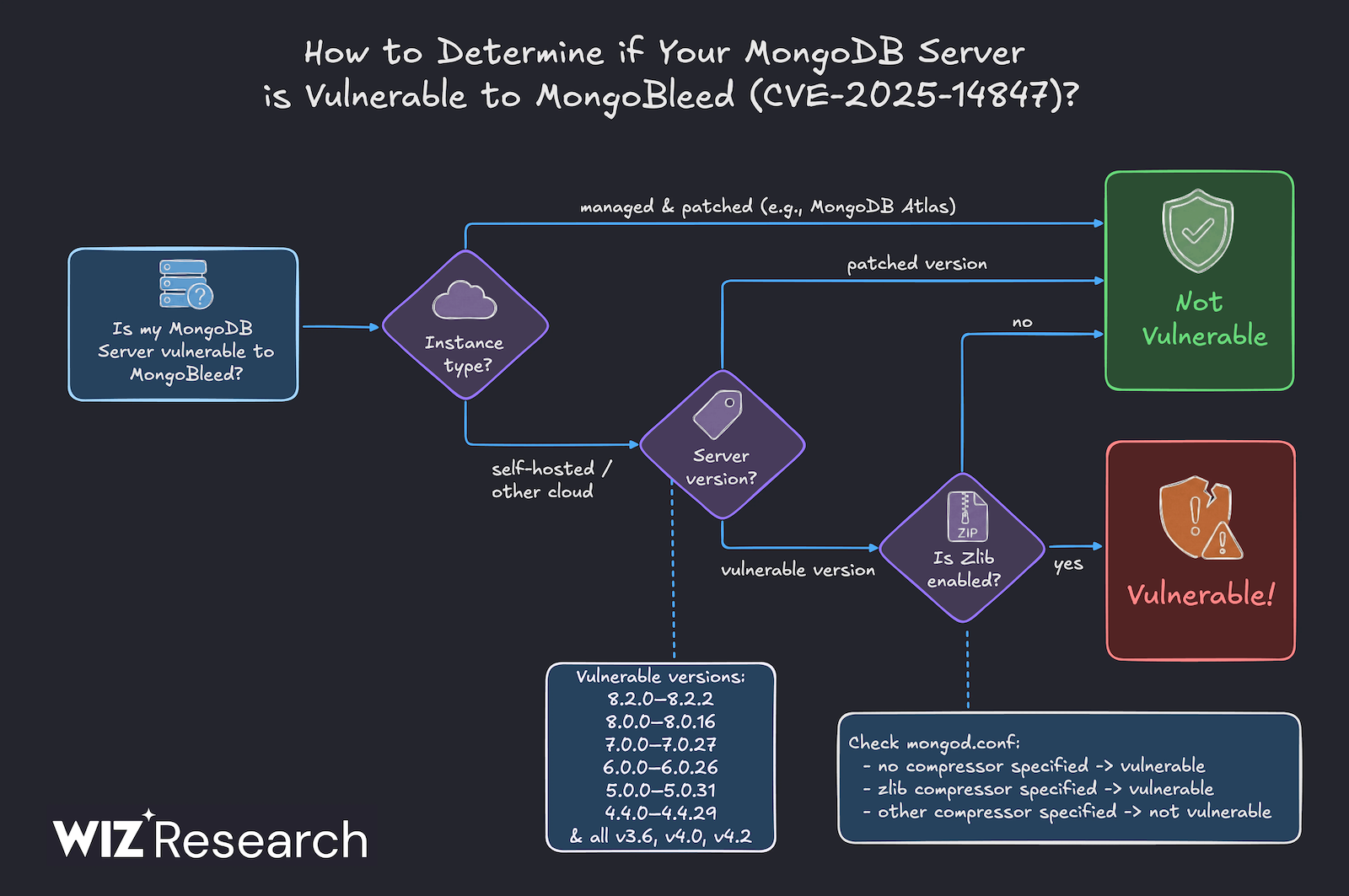
Are You Affected?
If you are running previous versions of OpenEverest with standard MongoDB configurations, you are likely vulnerable. The CVE affects the 8.0, 7.0, 6.0, 5.0, and 4.4 series.
The Fix: OpenEverest 1.12
OpenEverest orchestrates workloads using the Percona Operator for MongoDB. OpenEverest 1.12 updates core dependencies to use Percona Operator v1.21.2, which pulls patched Percona Server for MongoDB images.
According to the Percona Release Notes, this version addresses CVE-2025-14847 by using these safe versions:
- Percona Server for MongoDB 8.0.17-11
- Percona Server for MongoDB 7.0.28-10
- Percona Server for MongoDB 6.0.27-23
- Percona Server for MongoDB 5.0.32-28
- Percona Server for MongoDB 4.4.30-29
Action: Upgrading your cluster to OpenEverest 1.12 will automatically roll out these patched versions.
Mitigation (If You Cannot Upgrade Immediately)
If an immediate upgrade to 1.12 isn't possible due to change management windows, you can mitigate the vulnerability by changing your configuration:
- Disable zlib Compression: The vulnerability is specific to zlib. Update your ConfigMaps or arguments to remove zlib from networkMessageCompressors. Safe alternatives are snappy or zstd (or no compression).
- Isolate Traffic: Ensure strict NetworkPolicies are in place. MongoDB pods should never be exposed to the public internet via LoadBalancers or Ingress without strict IP whitelisting.
Solanica Platform: Enterprise Support
For teams running the Solanica Platform (our enterprise edition built on OpenEverest), we have released an update to the platform and you should follow the regular upgrade procedure.
This update includes automated upgrade workflows that help roll out the 1.12 patch across complex, multi-cluster self-hosted environments with minimal downtime. If you are a current customer and need assistance planning this upgrade for your production environments, please reach out to our support team directly.
Resources & Next Steps
- Open Source Users: You can find the release and upgrade instructions on the OpenEverest Website. For help or questions, join the discussion on our Community Page.
- Solanica Platform Inquiries: If you need help managing data workloads on Kubernetes or want to learn more about our enterprise security features, you can book a demo with us or contact the team directly.
